TT
Toufik Touhami
[ SECURITY RESEARCHER ]
Elite security researcher specialized in offensive operations and financial logic protection. Focused on high-impact vulnerability discovery.
WEB / APIBUG BOUNTYOFFENSIVE TESTING
STATUS: AVAILABLE FOR FREELANCE
Credentials // 02
+0Y
Experience
• SECURITY+
• CEH
• PNPT
Stats // 03
0+
Vulnerabilities
Impact // 04
$0M+
Assets Secured
Trusted_By +50 big companies // 05






















Workflow // 06
[01]
RECON
Asset discovery & surface mapping.
[02]
ANALYZE
Manual logic audit & API check.
[03]
EXPLOIT
PoC development & escalation.
[04]
REPORT
Remediation guidance & docs.
Recent_findings // 07
Blind XSS → Admin ATO CRITICAL
> Hijacked sessions via WAF bypass polyglots.
Withdrawal Logic Flaw CRITICAL
> Race condition exploitation in payment gateways.
IDOR: Private Billing Leak HIGH
> Compromised sensitive PII via UUID manipulation.
Services // 08
[+]
WEB APP PENTEST
Manual testing for critical web application flaws.
[+]
API SECURITY REVIEW
Access control, auth, and business logic validation.
[+]
ATTACK SURFACE REVIEW
Recon-focused review for exposed assets and risky paths.
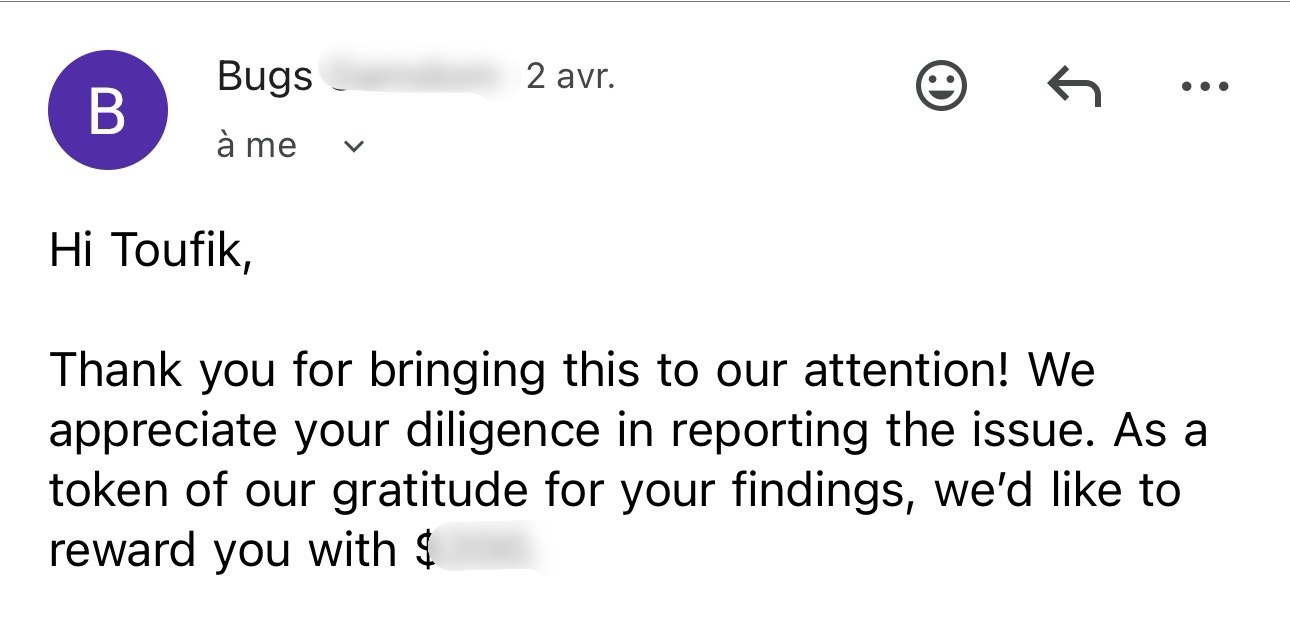
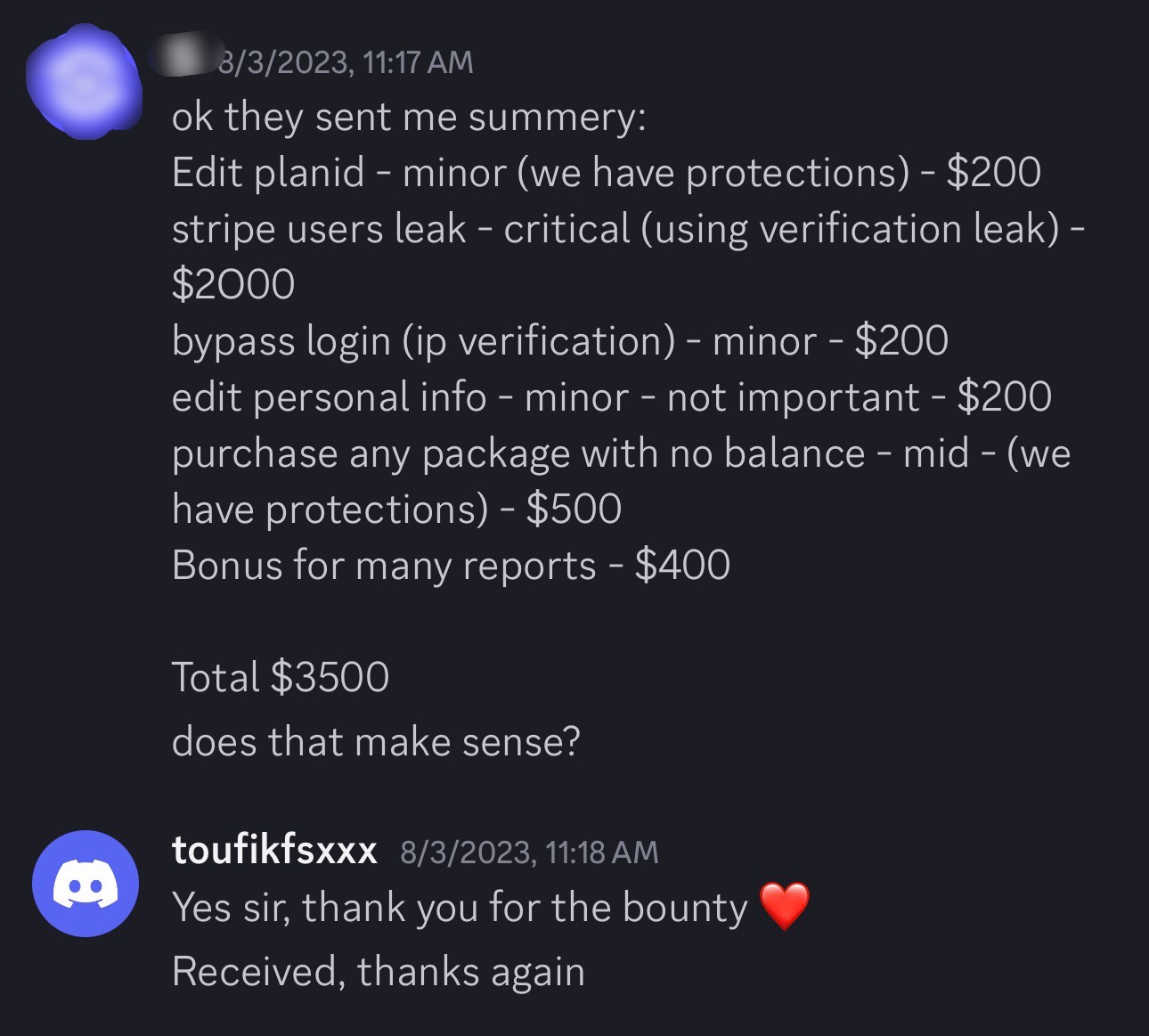
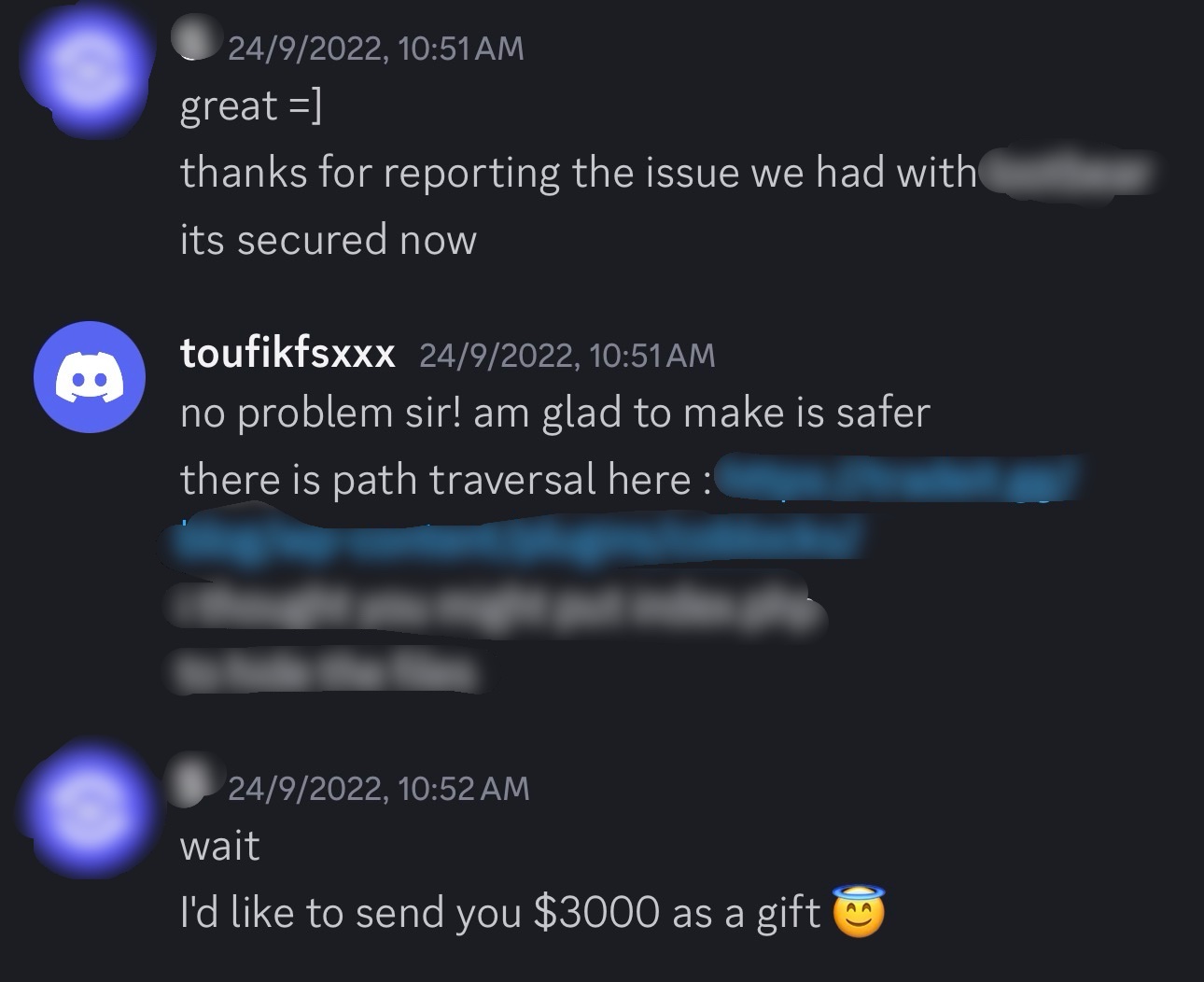
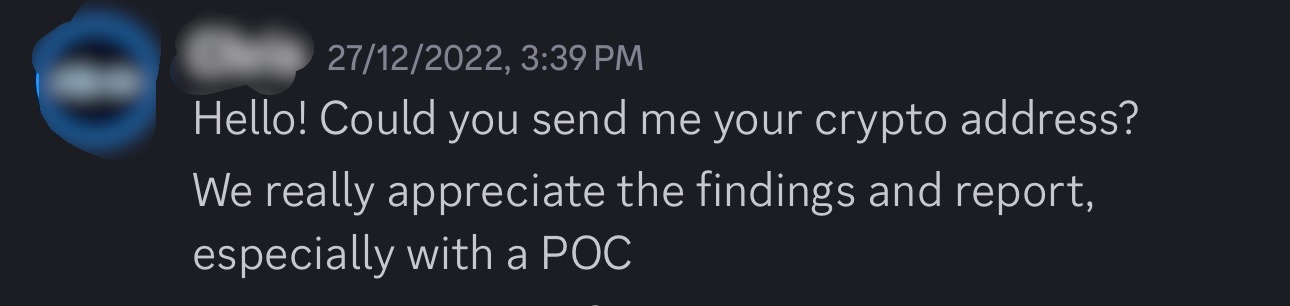
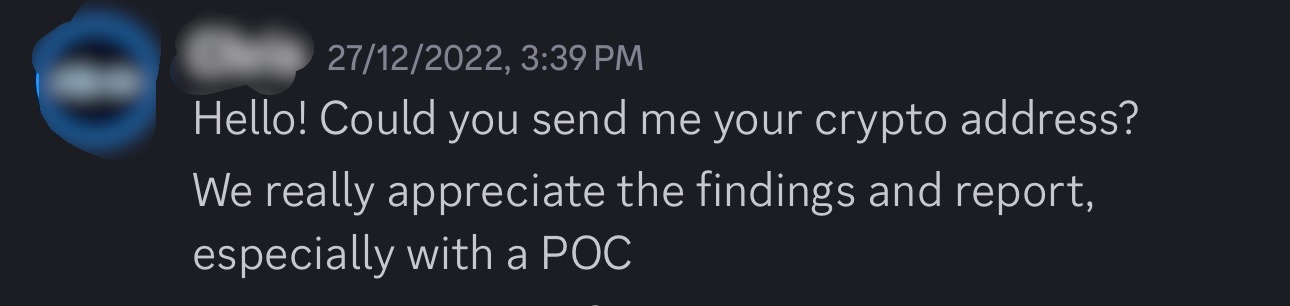
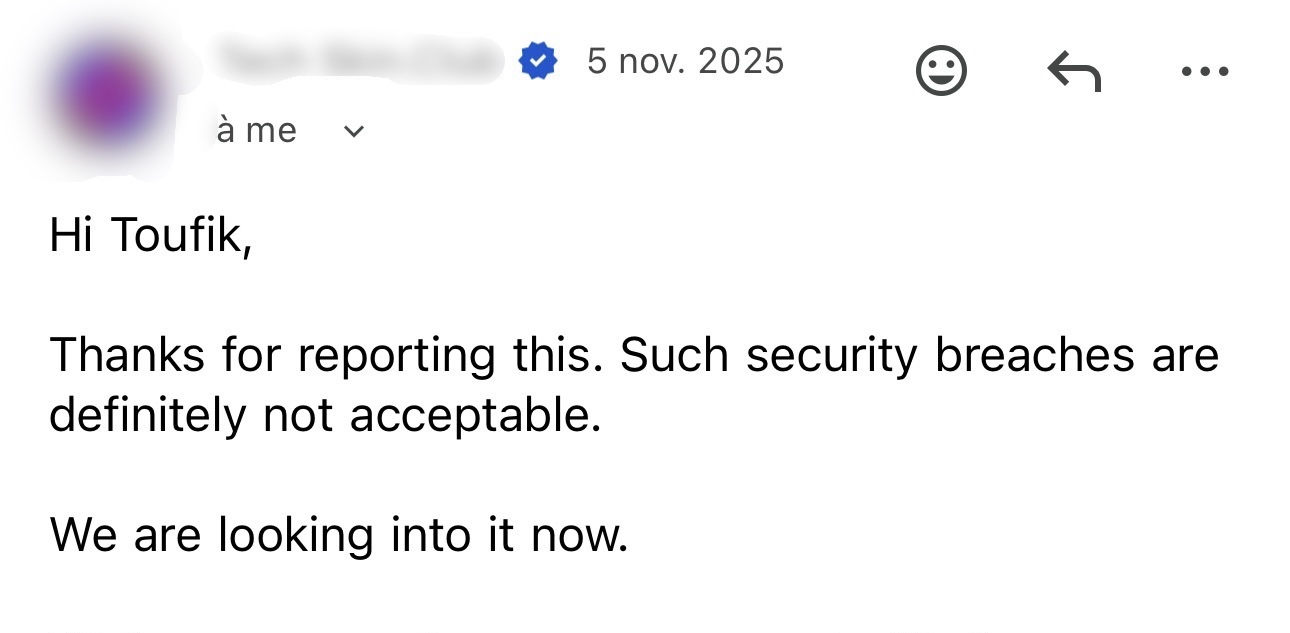
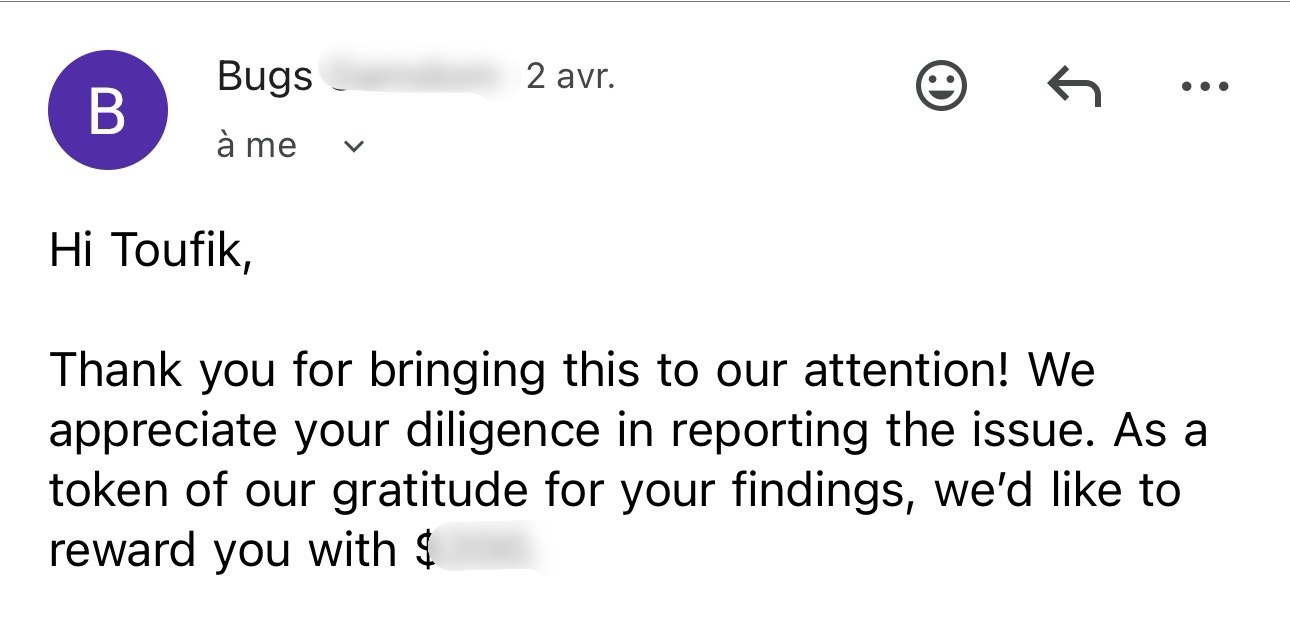
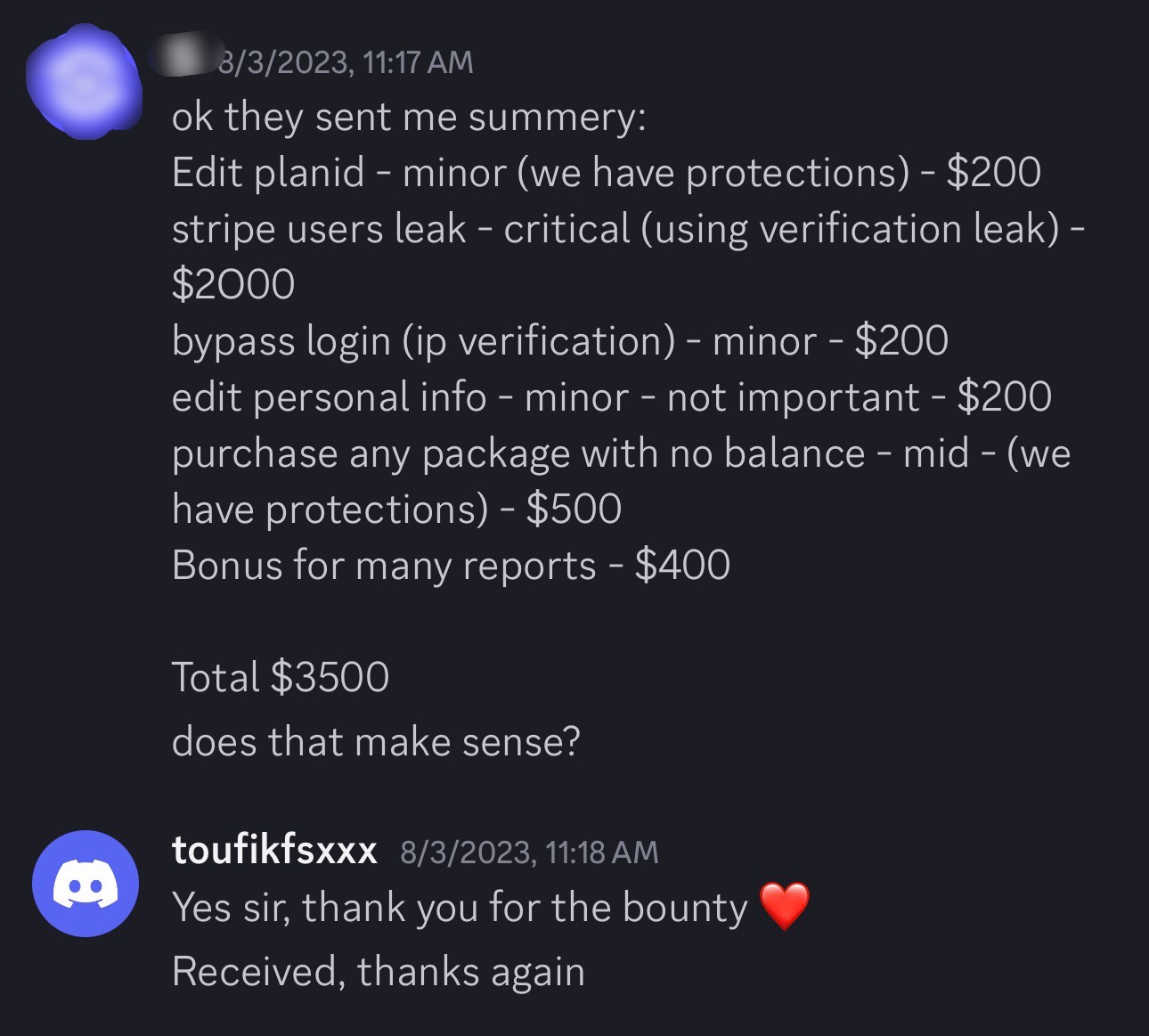
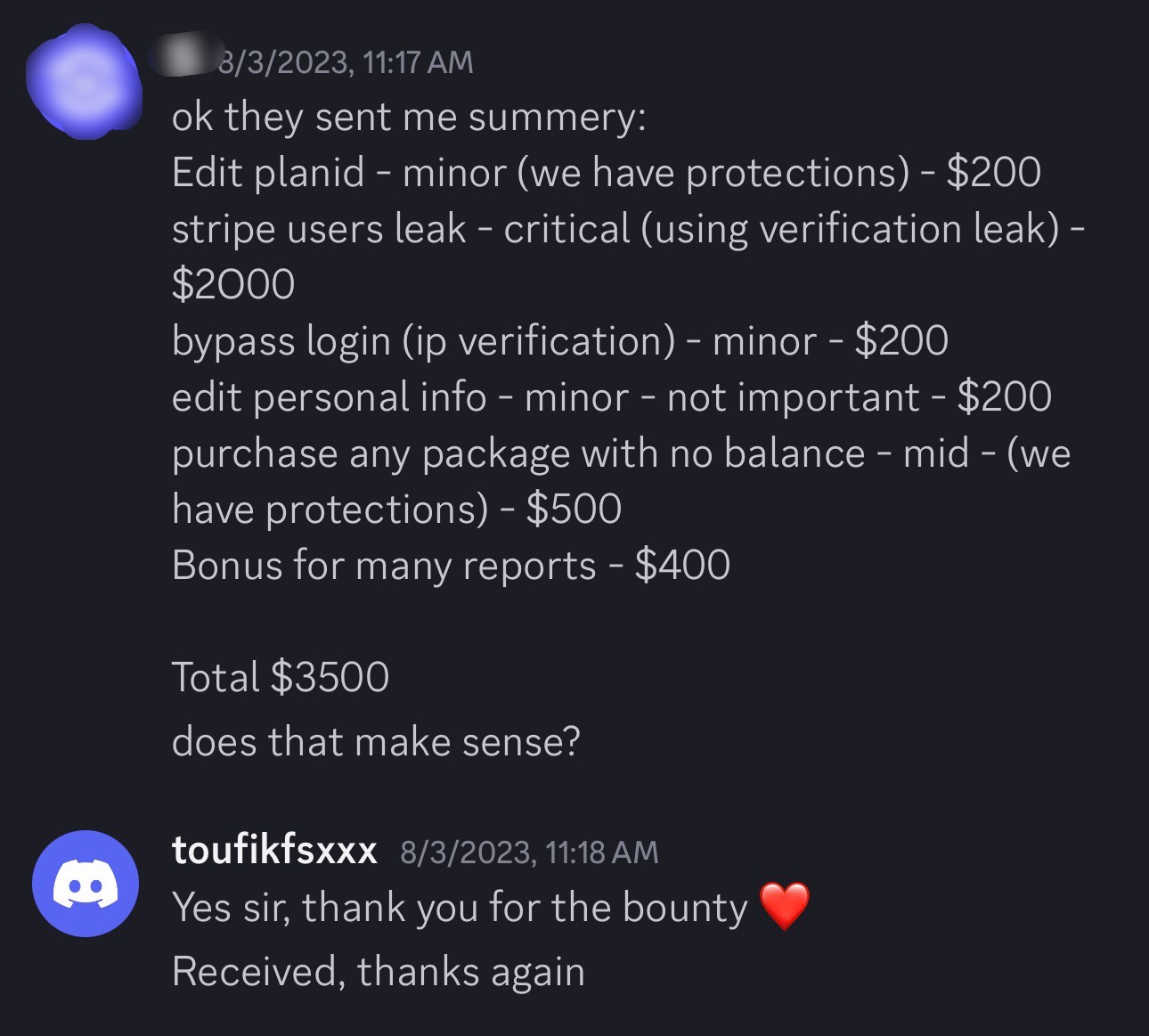
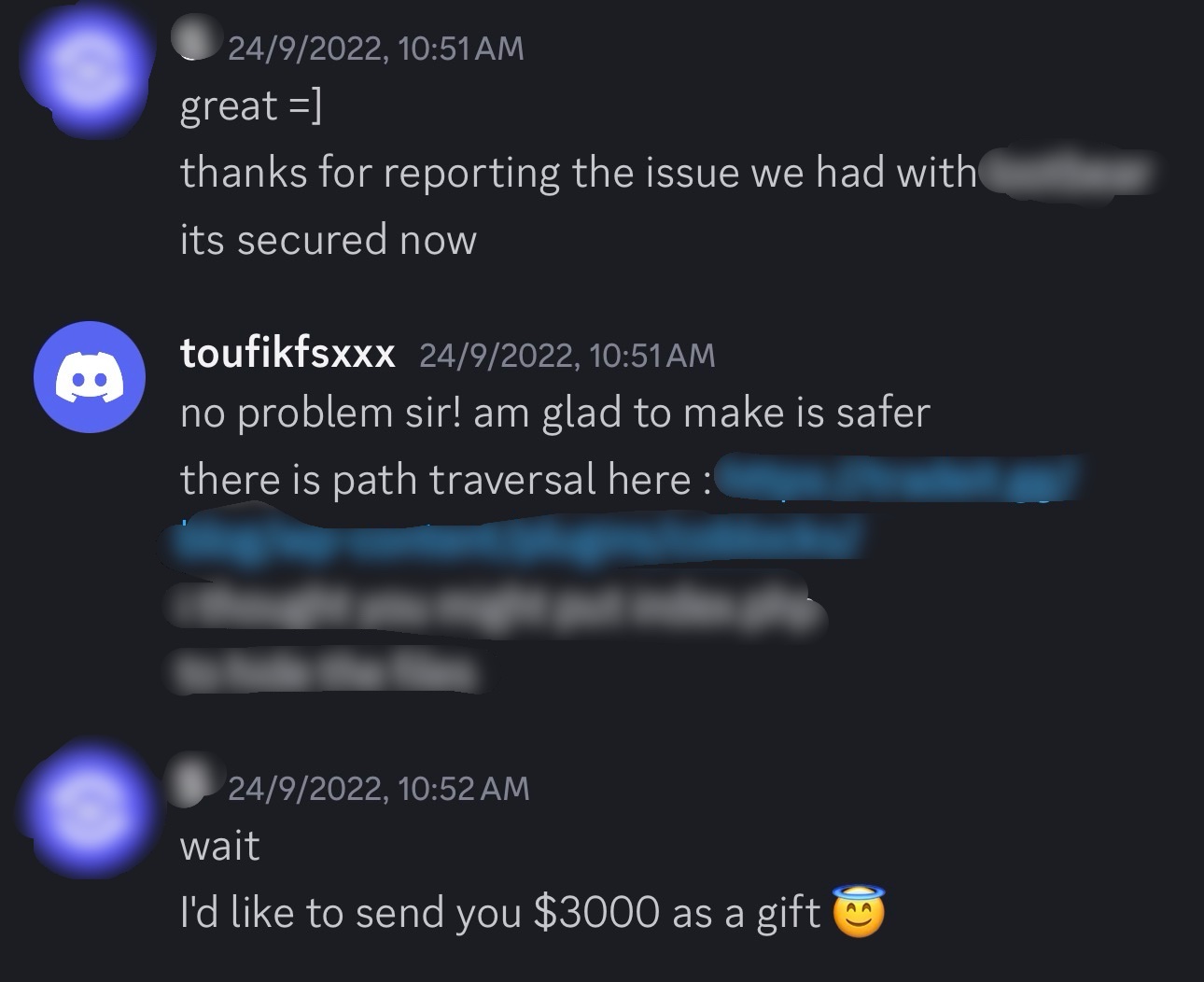
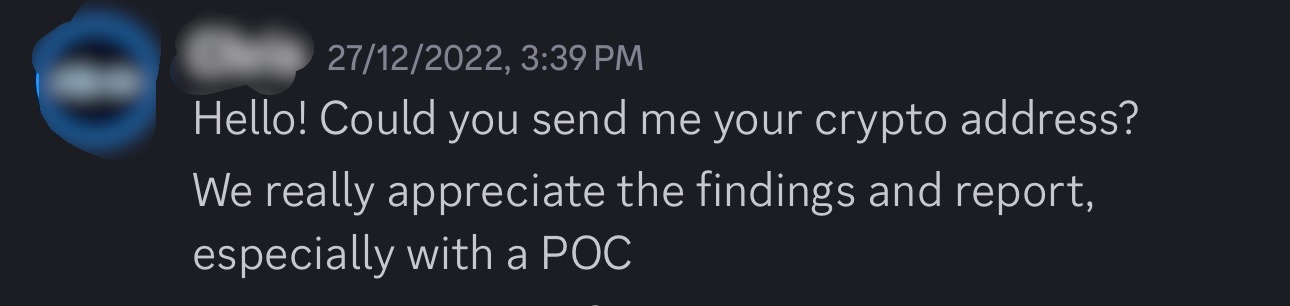
Bounty_Proofs // 09
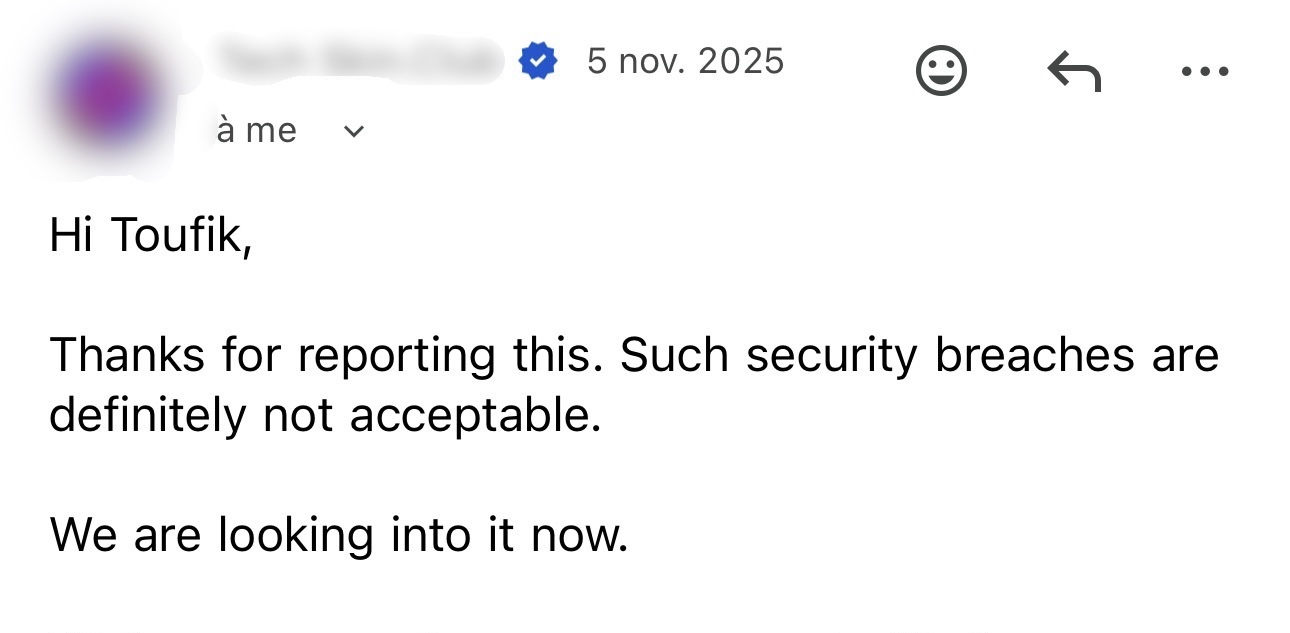
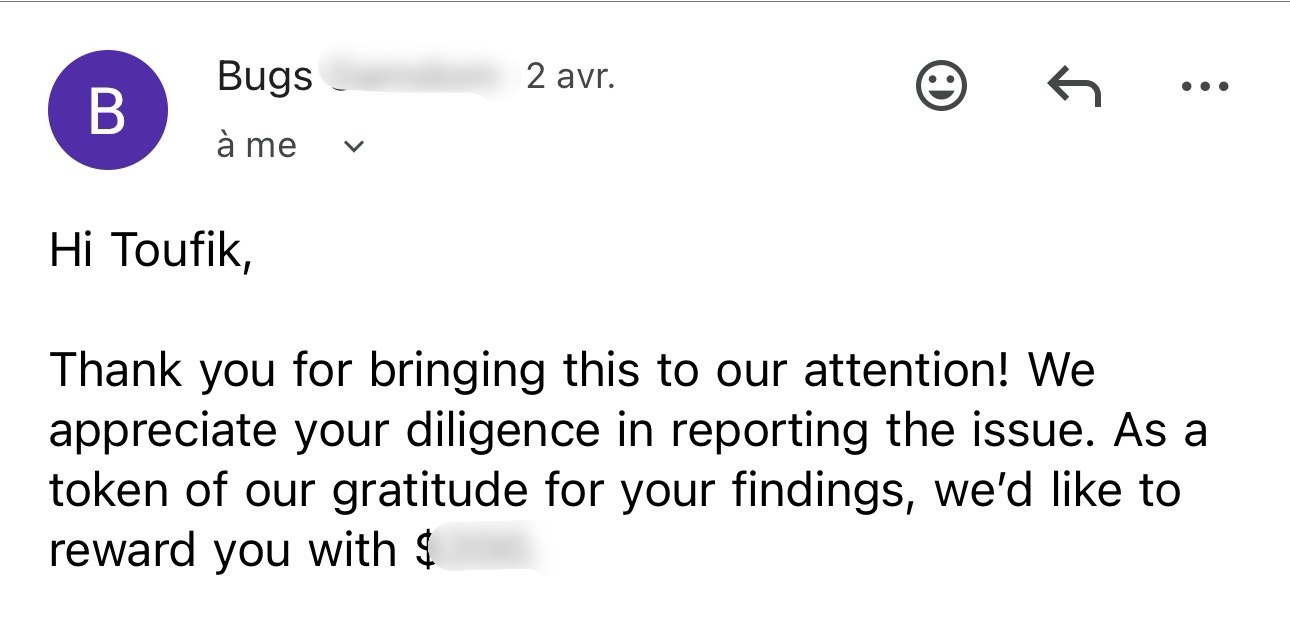
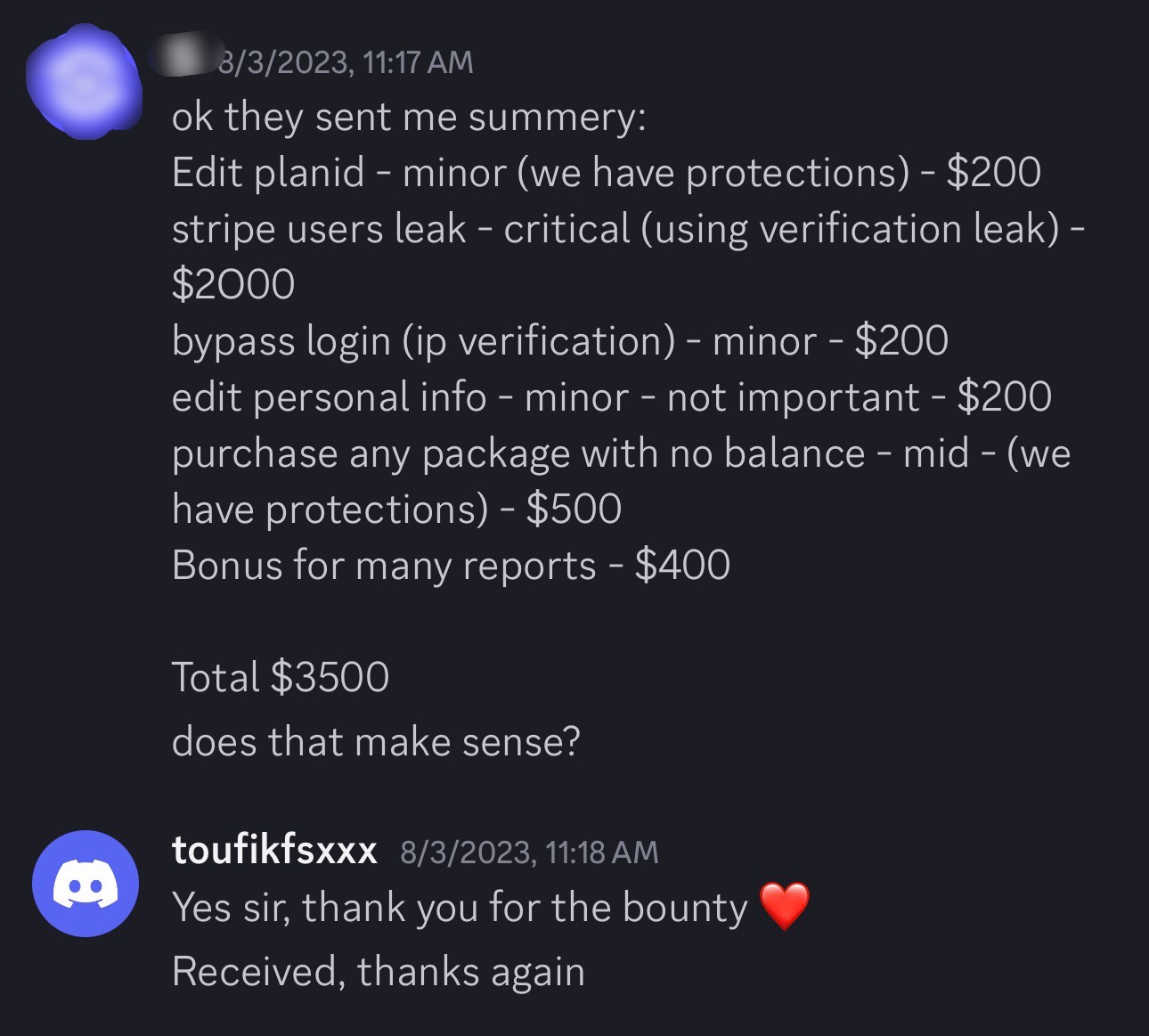
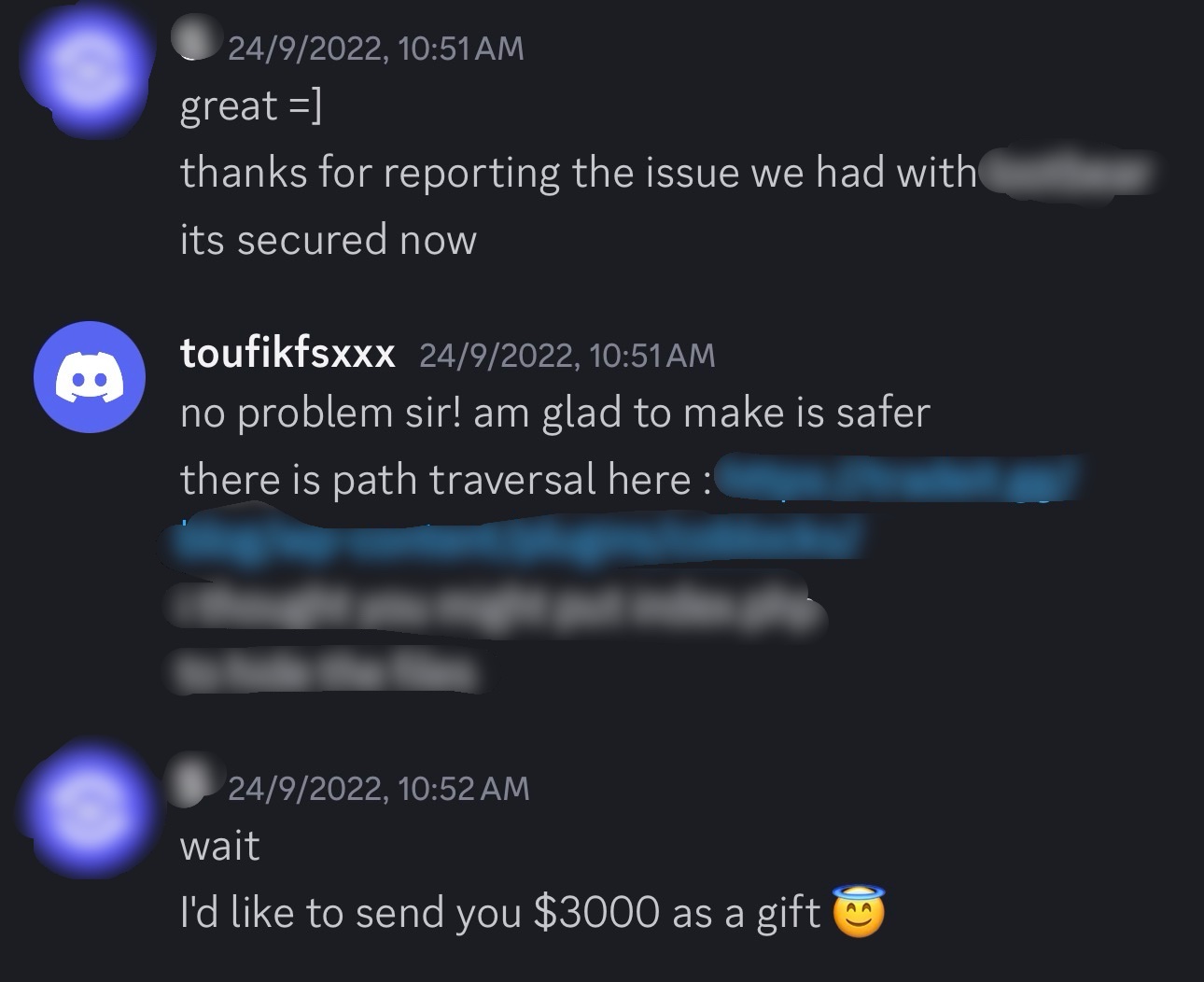
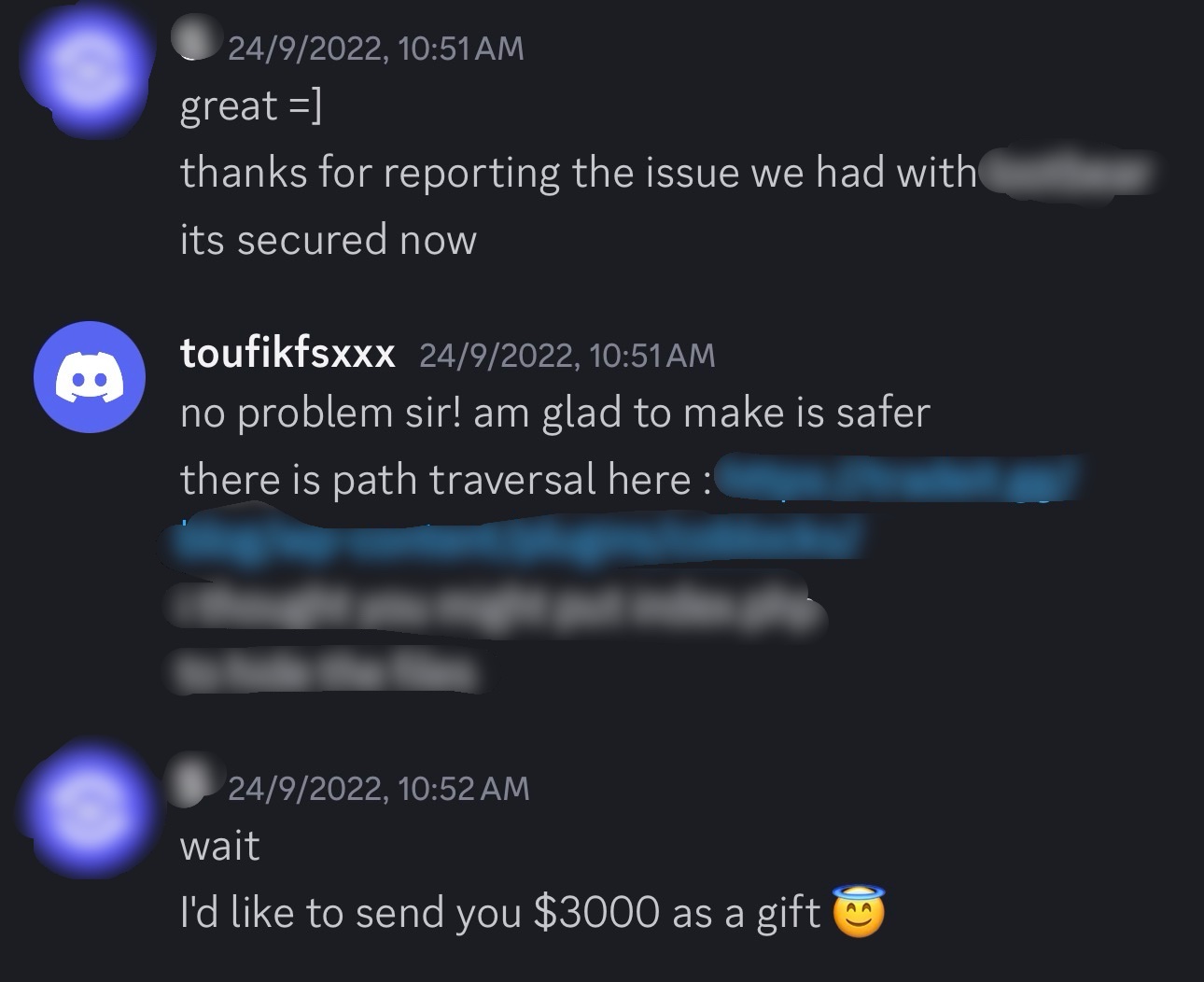
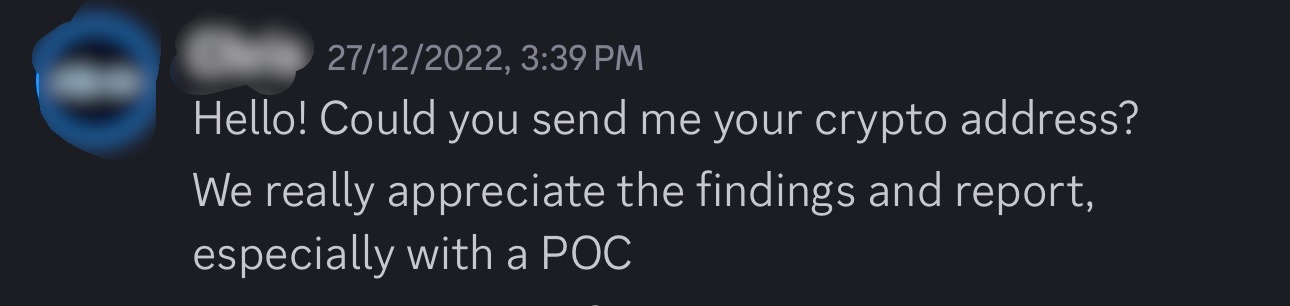
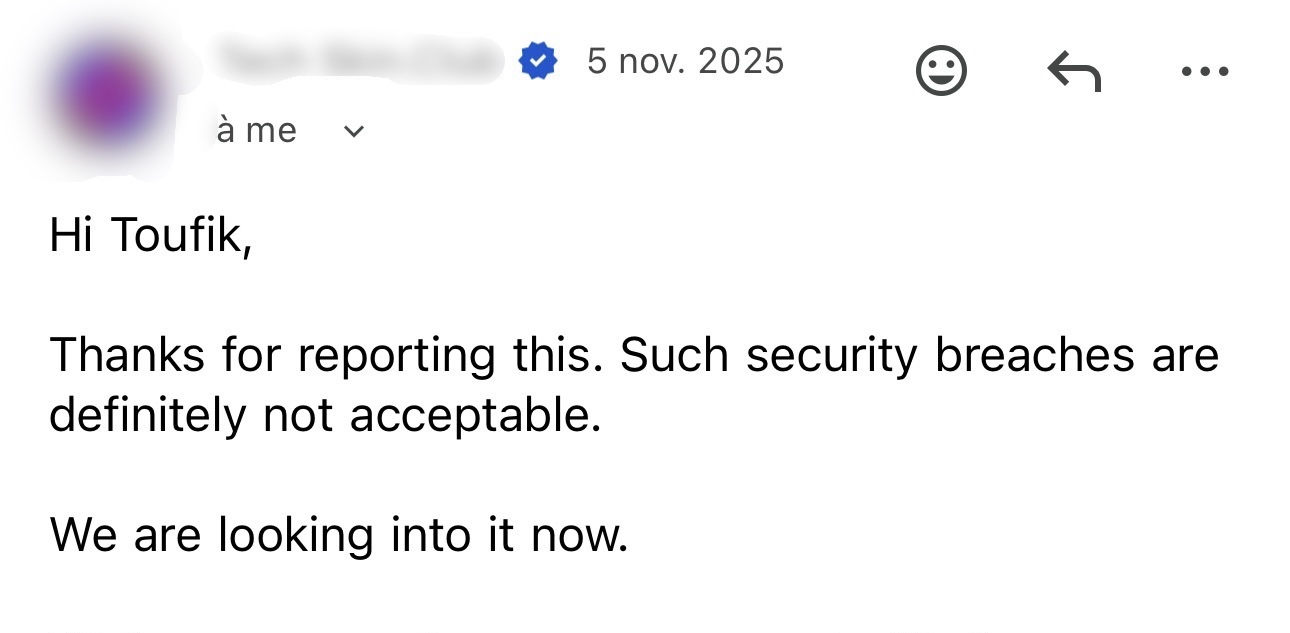
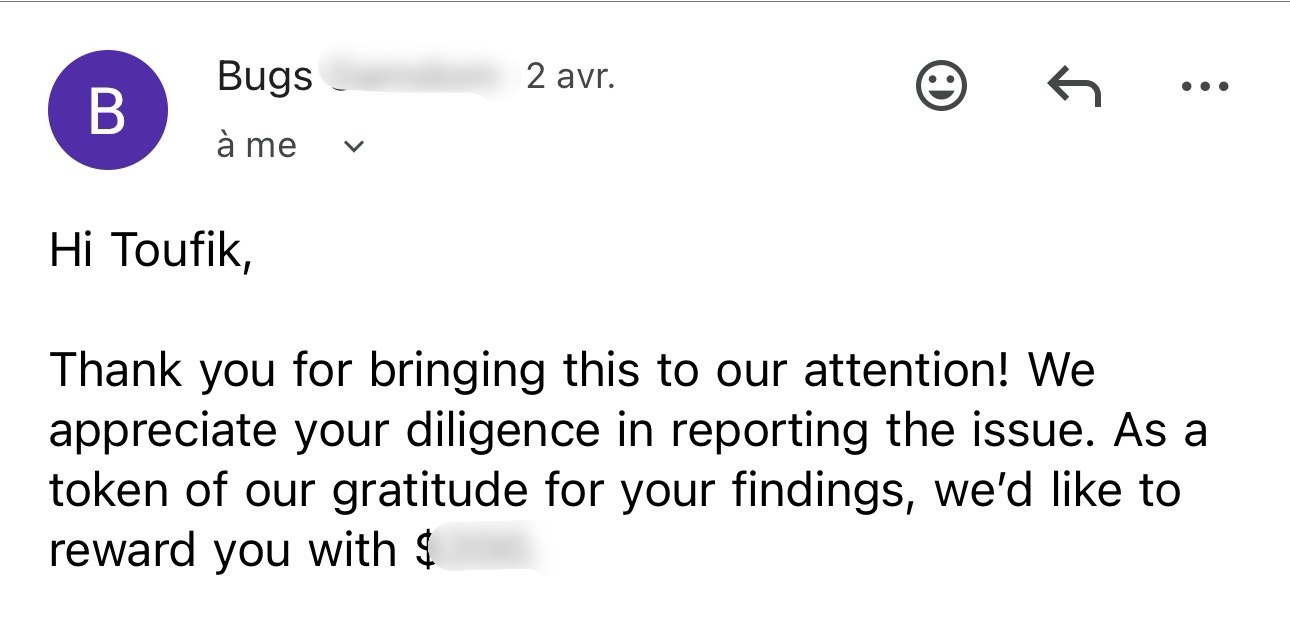
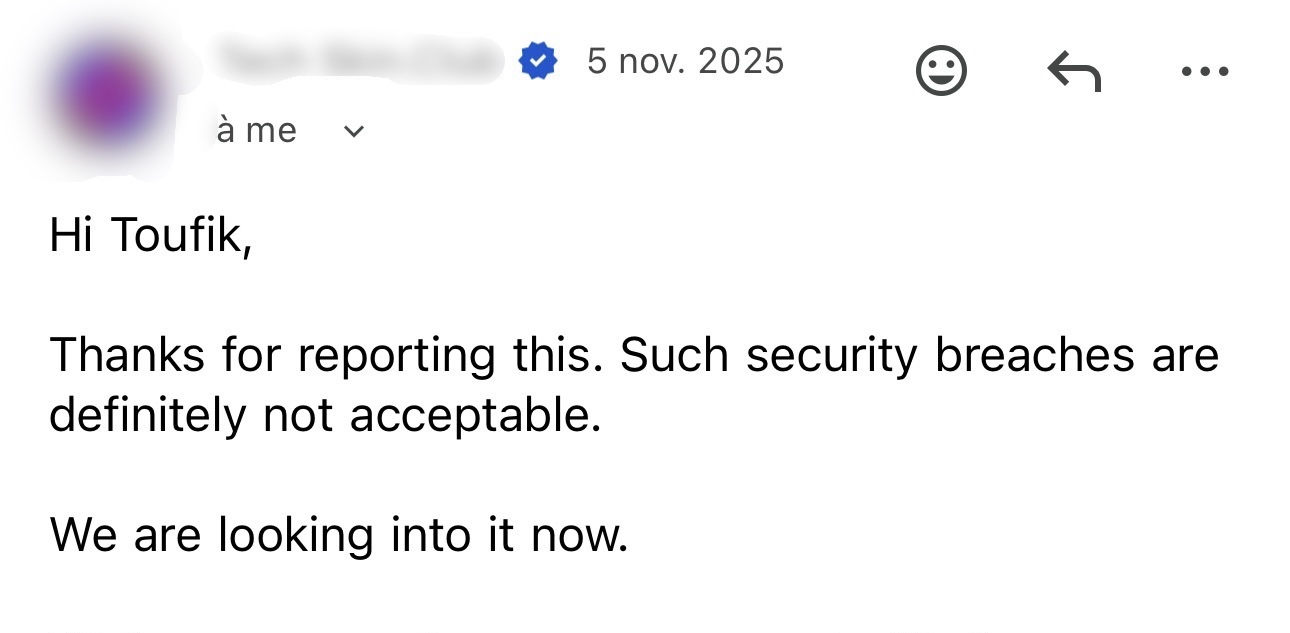
Program Feedback // 10
Fast validation & clear impact
> Triaged quickly with positive feedback on clarity and reproducibility.
High-signal reporting
> Detailed write-up helped the program verify risk and move to remediation faster.
Actionable research notes
> Feedback highlighted strong communication, practical PoCs, and useful technical context.
Contact // 11
> Spam protection is enabled. CAPTCHA must be completed before the form can be sent.
Featured_Report // 12
Multi-Vector Bypass & Response Manipulation → Infrastructure Takeover
CRITICAL (10.0)
> TARGET: redacted.com (+50k users)
> DISCOVERY: Inconsistencies in URL normalization between WAF and origin.
> BYPASS: Used /%2f%2f/ & case-sensitivity manipulation in API routes.
> ESCALATION: Leveraged Response Manipulation for Superadmin access.
> IMPACT: Tradebot control, user PII leak, and PayPal/Crypto approvals.
> DISCOVERY: Inconsistencies in URL normalization between WAF and origin.
> BYPASS: Used /%2f%2f/ & case-sensitivity manipulation in API routes.
> ESCALATION: Leveraged Response Manipulation for Superadmin access.
> IMPACT: Tradebot control, user PII leak, and PayPal/Crypto approvals.